Whole tech-aware internet these days is talking not only about bending iPhone 6, but also a serious vulnerability in Bash which may allow custom command injection hack thus gaining access and usually root to your box. Here are some tips on checking your system.
Red Hat reports that:
The bash code injection vulnerability CVE-2014-6271 could allow for arbitrary code execution, allowing an attacker to bypass imposed environment restrictions. Certain services and applications allow remote unauthenticated attackers to exploit this vulnerability by providing environment variables. As the Bash shell is the most commonly used shell today, the risk of impact from this vulnerability if left unchecked could be severe.
I am not going to cover the vulnerability itself as it has been well explained by Wired and Kaspersky in both non and technical ways. Here are some tips to check your box.
Login to your system and execute following code suggested by DigitalOcean:
If you see following in output, means your system is vulnerable:
Bash Test[/code]
My
bash: error importing function definition for `VAR’
Bash Test[/code]
There are also several testing tools available:
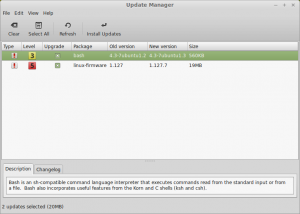
To secure your system, make sure to “yum update” your

Leave A Comment